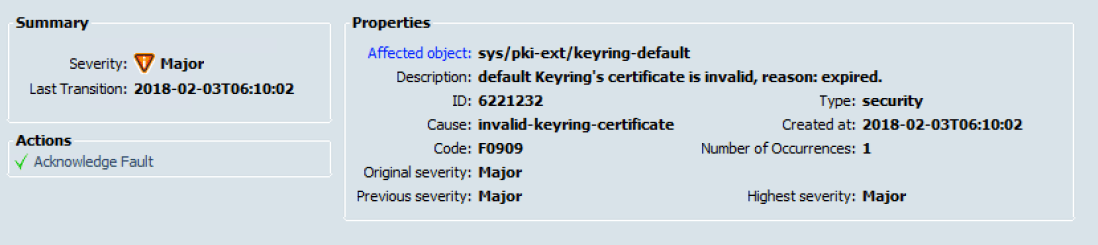
The default (self-signed) UCSM keyring certificate must be manually regenerated if the cluster name changes or the certificate expires. The default certificate is valid for one year. Ideally you have replaced the default certificates but if you haven’t then you will see the following Major alert in UCS Manager when the certificate expires :
The fix is pretty simple. This process doesn’t cause any cluster outage or downtime but ensure you have a valid change raised in your change management system.
Here are the steps:
- Make sure Fabric Interconnects have correct time settings. It is best if they are synchronized with NTP server. This can be checked in UCS Manager. Go to Admin tab then ‘All’ dropdown and pick Timezone Management. Details for NTP will be in there.
- If all looks well then SSH to the UCS Manager Cluster IP of the UCS Domain. Make sure the user has admin credentials. If you are using the local admin account the following syntax might need to be used
- Putty Session
login as: ucs-local\adminCisco UCS 6100 Series Fabric InterconnectUsing keyboard-interactive authentication.Password:xxxxxxxx- Mac Terminal Session
ssh ucs-local\\admin@192.16060.1Cisco UCS 6100Series Fabric InterconnectPassword:xxxxxxxxx- Once logged in run the following commands to regenerate the certificate
dev1-ucs-1-B# scope security dev1-ucs-1-B /security # scope keyring default dev1-ucs-1-B /security/keyring # set regenerate yes dev1-ucs-1-B /security/keyring* # commit-buffer - After you issue ‘
commit-buffer‘ command, all GUI sessions will be disconnected. Log back onto the UCSM and accept new certificate. The Major error should be gone but it can take a few minutes to disappear - To verify the new certificate is validated it can be checked by running the following in putty or terminal
dev1-ucs-1-B /security/keyring* # scope security dev1-ucs-1-B /security* # show keyring detail- If the certificate has been generated correctly the you should get something similar to the following output
dev1-ucs-1-B /security* # show keyring detail Keyring default: RSA key modulus: Mod1024 Trustpoint CA: Cert Status: Self Signed Certificate Certificate: Data: Version: 3 (0x2) Serial Number: ec:6d:02:ca:1b:96:4c:2e Signature Algorithm: sha1WithRSAEncryption Issuer: CN=dev1-ucs-1-b Validity Not Before: Jun 18 13:35:49 2015 GMT Not After : Jun 17 13:35:49 2016 GMT Subject: CN=dev1-ucs-1-b Subject Public Key Info: Public Key Algorithm: rsaEncryption RSA Public Key: (1024 bit) Modulus (1024 bit): 00:c5:c2:b8:d6:8b:06:e3:9a:3a:4b:d2:cf:e3:58: 45:31:d9:e1:ef:0d:4b:ba:42:98:90:52:46:d3:a1: 8b:a8:a5:97:6e:fe:1d:df:34:82:21:73:b0:20:1b: 8e:da:eb:a3:5d:13:46:d0:fe:f8:91:f8:1d:0d:6f: 41:2f:23:dc:96:47:9f:f2:5e:df:5a:08:94:3f:2c: 1d:c8:d1:35:ce:83:5e:03:d3:9c:a7:81:0c:67:3b: d8:1f:94:43:46:d9:8b:0e:dc:f6:d9:41:4e:d4:64: bc:12:67:82:78:f0:00:71:6e:ef:a9:38:cb:f9:c0: 3c:f6:cd:15:66:48:94:59:99 Exponent: 65537 (0x10001) X509v3 extensions: X509v3 Subject Alternative Name: critical DNS:dev1-ucs-1-b.dev.local, IP Address:192.168.60.1, IP Address:192.168.60.2, IP Address:0:0:0:0:0:0:0:0 Signature Algorithm: sha1WithRSAEncryption b7:d9:64:41:24:08:cc:45:2d:a3:4e:c9:66:96:dc:1b:40:8d: ad:1b:72:55:0f:70:93:d1:a4:77:65:be:9d:d7:d4:00:b6:de: 34:03:d4:c7:a2:01:7d:65:7f:ba:8f:95:d1:0e:ee:bf:eb:b4: 18:5f:15:26:51:9f:cf:34:33:bd:92:39:d2:12:f0:06:1f:ea: 16:60:e1:9d:e8:26:32:99:fe:b5:75:0a:fa:ee:ac:f3:e0:32: f4:f3:51:65:1f:bf:0c:9b:3b:d3:9b:1c:dd:a2:cb:a8:86:45: e3:b5:ef:2b:bc:83:69:c5:f6:66:6a:7a:b9:2a:79:f0:74:7e: ab:ca -----BEGIN CERTIFICATE----- MIIB9TCCAV6gAwIBAgIJAO1tAsoclkwuMA0GCSqGSIb3DQEBBQUAMBcxFTATBgNV BAMTDGRldjEtZmktMWItYjAeFw0xNTA2MTgxMzM1NDlaFw0xNjA2MTcxMzM1NDla MBcxFTATBgNVBAMTDGRldjEtZmktMWItYjCBnzANBgkqhkiG9w0BAQEFAAOBjQAw gYkCgYEAycK41osG45o6S9LP41hFMdfh7w1LukKYkFJG06GLqKWZbv4d3zSCIXOw IBuO2uujXRNG0P74kfgdDW9BLyPclkef8l7fWgiUPywdyNE1z4NeA9Ocp4EMZzvY H5RDRtmLDtz22UFO1GS8EmeCePAAcW7vqTjL+cA89s0VZkiUWZkCAwEAAaNJMEcw RQYDVR0RAQH/BDswOYIZZGV2MS1maS0xYi1iLmlnaS5pZy5sb2NhbIcECv9rKIcE Cv9rKocQAAAAAAAAAAAAAAAAAAAAADANBgkqhkiG9w0BAQUFAAOBgQC32WRBJAjM RS2jTslmltwbQI2tG3JUD3CT0aR3Zb6d19QAtt40A9THogF9ZX+6j5XRDu6/67QZ XxUmUZ/PNDO9kjnSEvAGH+oWYOGd6CYymf61dQr67qzz4DL08lFlH78MmzvTmx3d osuohkXjte8rvINpxfZmanq5KnnwdH6ryg== -----END CERTIFICATE-----
One thought on “Regenerate Expired Cisco UCS Certificate”